By Mitch Christian, IT Security Director – CISSP, CISM
As the world becomes more and more virtual, the importance of data privacy and protection grow exponentially.
Synergy—a global organization with hundreds of trillions upon trillions of bits of data passing through its servers daily—works hard to adapt and ensure data is secure and protected. But, as with anything we do, it isn’t just about the measures we take.

It is about a security philosophy and culture hasten by a client base comprised of the world’s leading technology companies. It is about the purity of innovation. And, of course, it’s about partnership and trust.
It is there—at the crossroads of action, protocol, philosophy, and culture—one can begin to grasp the vision behind Synergy’s evolving data privacy and protection policies and procedures.
Holistic Approach
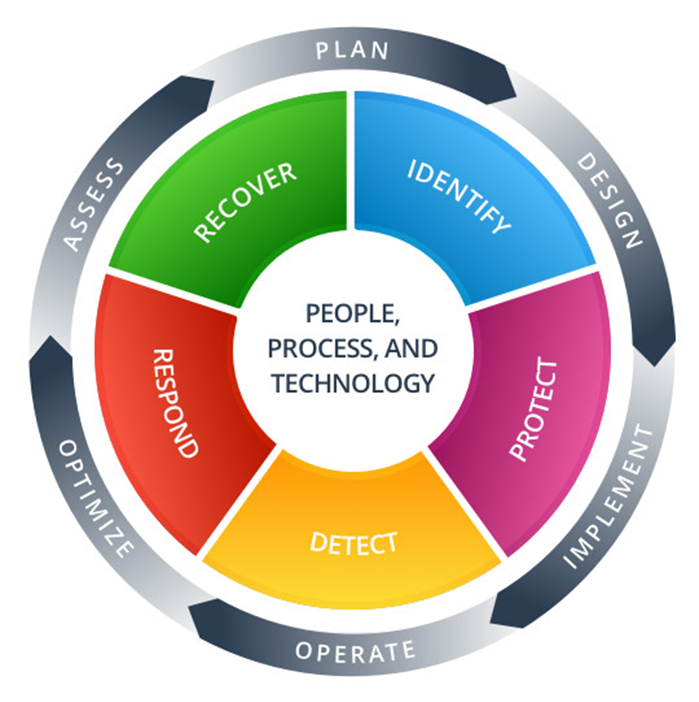
At Synergy, Cyber Security is governed by a holistic approach. First and foremost, we must consider the multiple components and programs used to operate the business. Those components and programs are then set in context to the overall security landscape and, most importantly, how we envision that landscape maturing in conjunction with our technology roadmap. Next, we consider and analyze potential risks and threats across our components and programs to ensure resources are allocated properly.
Overall, we are constantly assessing our security environment for new and on-going threats to facilitate a cohesive, agile security program.
Security Culture
We believe a successful data security program must start with culture. Synergy runs monthly phishing tests to build awareness, educate, and develop an understanding of the risks inherent in email. Moreover, we run multiple awareness campaigns throughout the year highlighting specific threats and tactics bad actors may use to gain access to our systems.
These efforts work to engage and familiarize the staff with social engineering techniques used to trick people into giving up information. We believe that by making terms such as phishing, malware, and data security part of the corporate lexicon, we have a foundation to support data responsibility and accountability across the entire workforce. In the end, Security is everyone’s responsibility. Peer-to-peer trust and responsible data security habits are our ultimate objectives.
Framework
Fundamentally, the structure of Synergy’s data security program is a security framework. That framework not only supports our general Security Program, it also provides the necessary guidance required to evolve and execute security fundamentals such as Identity Management, Access Control, and best practices for Incident Response.
The framework is also used to track the security program’s maturity and offers a quasi-scoring matrix to rate the program’s controls (i.e., metrics, KPIs, and the computing practices controls used to ensure unauthorized parties do not access data.)

Encryption
Strong encryption is used in multiple forms to help protect data. Whether our data is stored or in transit, data security best practices for encryption are deployed for data protection and compliance.
Compliance
Synergy follows multiple compliance standards such as SOC2, GDPR, CCPA, and PCI-DSS. Compliance goes hand and hand with the security framework noted earlier. These compliance standards ensure proper protection is put in place to protect data, privacy, and personal information.

To some, bits of data are like the tiny atoms coursing throughout our bodies. From that lens, it is easy to see how Cyber Security is a living, breathing entity. It is never stagnant, always changing, and requires constant assessment to protect the organization and our client’s data.
Different methods of compromise and attack are consistently being thought up and executed by bad actors. These Bad Actors are smart, cunning, and well-incentivized. But by taking a structured approach to data security—one rooted in philosophy, culture, and the power of the collective—Synergy protects our user’s privacy and data doing its part to be the responsible partner our clients and guests deserve.


